Hardened supply chain
We protect your equipment from the factory to your door. Our process prevents tampering to ensure your security is never compromised.
Native self-custody
You own your keys and your digital sovereignty. We provide the tools to help you manage your assets and eliminate third party risk entirely.
Verifiable reputation
The timeline provides the ultimate consensus. We share public reviews so you can see how we perform for the community.
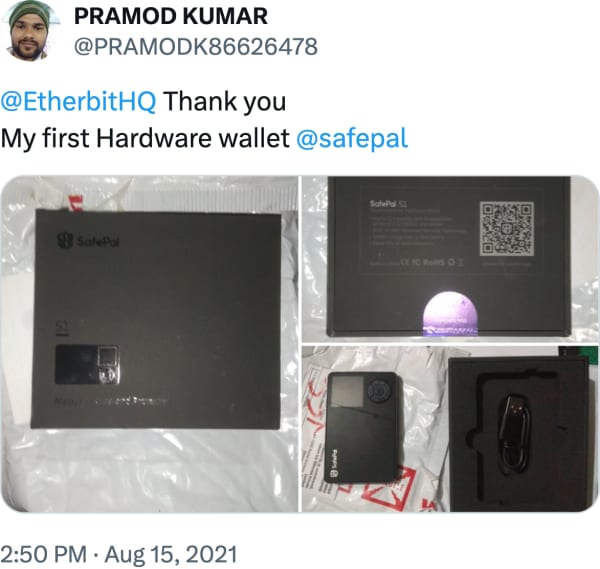
Fans in India interested in @safepal S1 Hardware Wallet can visit @EtherbitHQ @EtherbitHQ is an official reseller of @safepal in India
Read full review on XAs holding crypto on exchanges or wallets can be risky, they found a business opportunity in retailing hardware crypto wallets in India. Now, they're excited about India's exponential adoption of #crypto. @dhvani__v @EtherbitHQ @harshjv @rishabhmansur2 https:// yourstory.com/2021/08/hardwa re-crypto-wallet-etherbit-startup-trezor-ledger/amp …
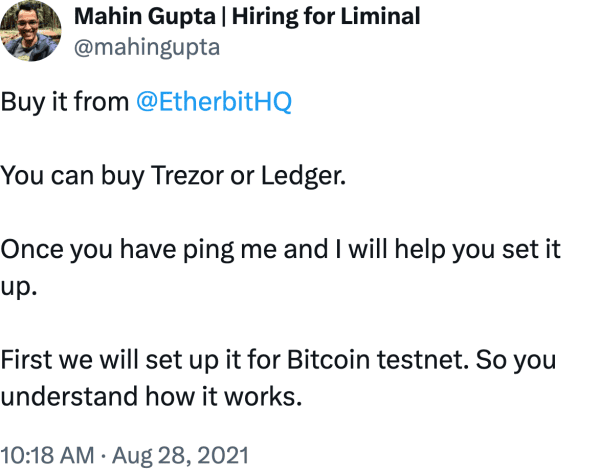
Read full review on XBuy it from @EtherbitHQ You can buy Trezor or Ledger. Once you have ping me and I will help you set it up. First we will set up it for Bitcoin testnet. So you understand how it works.
Read full review on XTangem Wallet is available in India through our official reseller, @EtherbitHQ https:// etherbit.in/products/tange m-wallet … Get secure card sets with trusted local service and fast delivery — the easiest way to take full control of your crypto.
Read full review on XWe'd like to welcome our new reseller @EtherbitHQ Check them out here: https:// etherbit.in/products/shift crypto-bitbox …
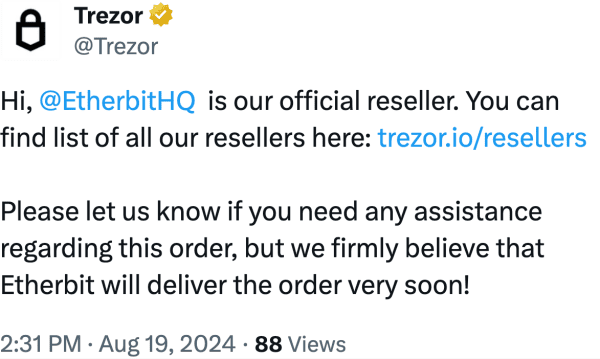
Read full review on XHi - yes, Etherbit is an authorized reseller. You can find a full list of approved resellers here:
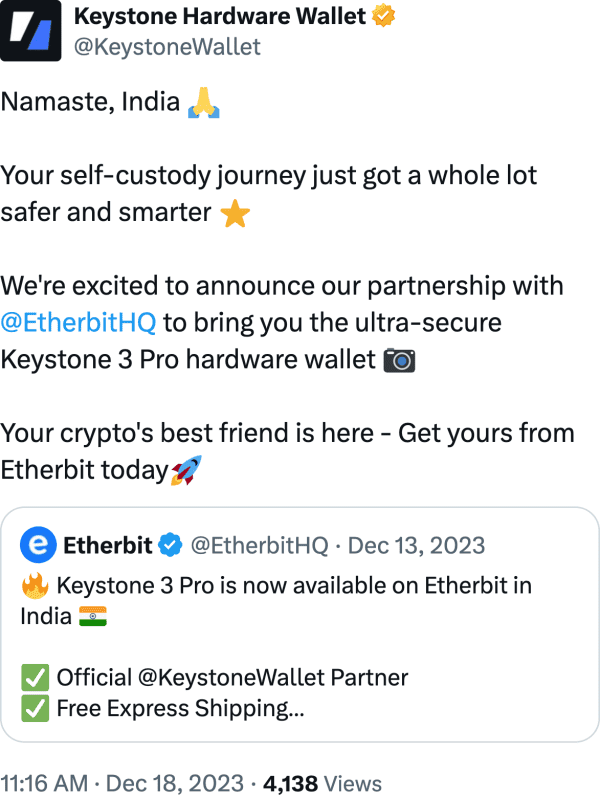
Read full review on XNamaste, India Your self-custody journey just got a whole lot safer and smarter We're excited to announce our partnership with @EtherbitHQ to bring you the ultra-secure Keystone 3 Pro hardware wallet Your crypto's best friend is here - Get yours from Etherbit today
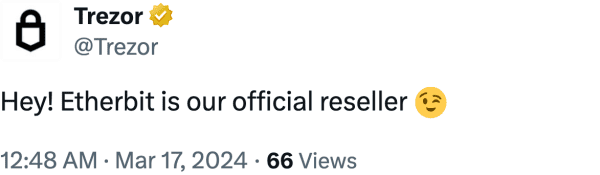
Read full review on XYes, @EtherbitHQ is our official reseller, you can find a complete list of them at https:// trezor.io/resellers/
Read full review on XLast week at India Blockchain Week What an amazing experience and vibrant market. Thanks for the great collaboration with @Ledger - @IBWofficial , @Transak & @onmetahq , @EtherbitHQ
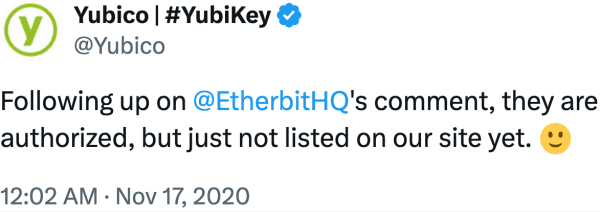
Read full review on XFollowing up on @EtherbitHQ 's comment, they are authorized, but just not listed on our site yet.
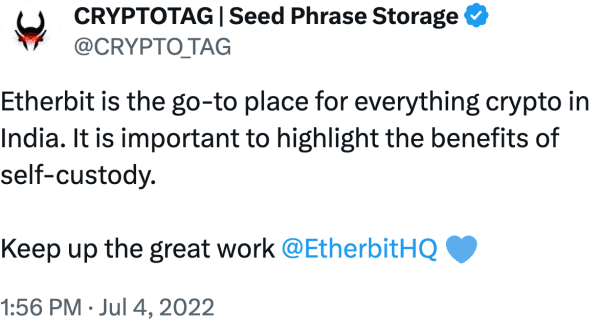
Read full review on XEtherbit is the go-to place for everything crypto in India. It is important to highlight the benefits of self-custody. Keep up the great work @EtherbitHQ
Read full review on XYay... hardware wallet has arrived Ledger Nano S @EtherbitHQ
Read full review on XYes, paper pe and then laminate that paper or keep it in a zip pouch. But the best way is to buy a metal plate @EtherbitHQ
Read full review on XA comprehensive video for all the beginners in crypto on how to store your crypto in a safe and secure manner. In this video, we were joined by Harsh, founder of @EtherbitHQ who provides security solutions for crypto storage in India. A Must Watch https:// youtu.be/ZuhHs1ybPeA
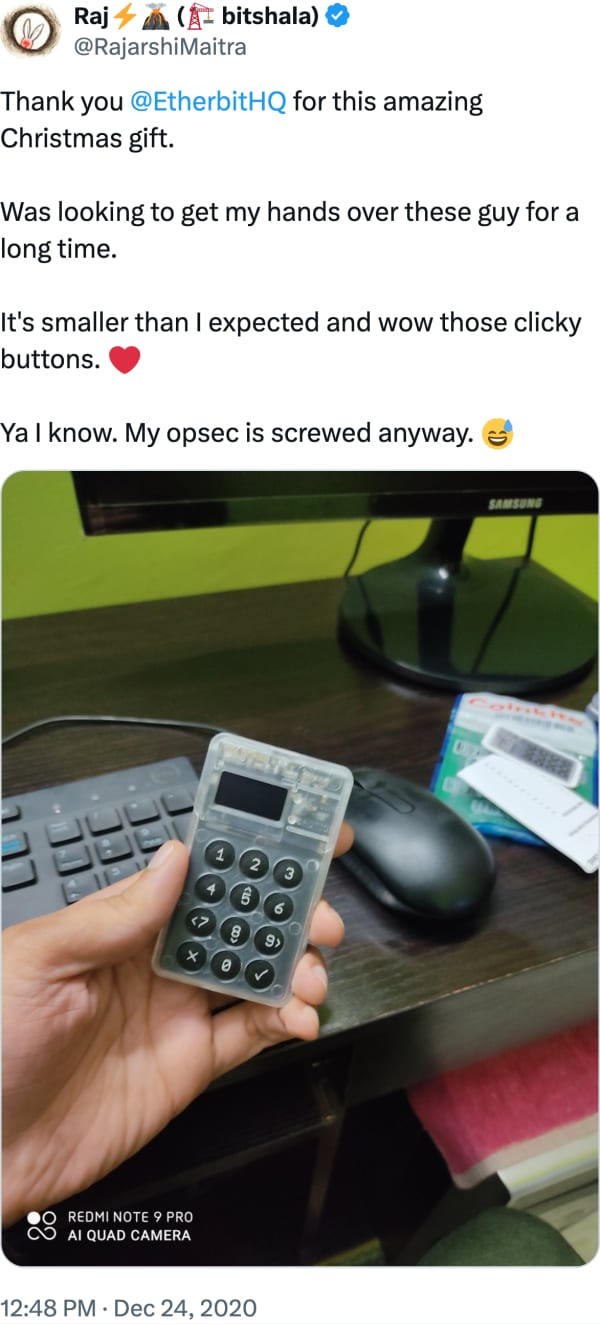
Read full review on XThank you @EtherbitHQ for this amazing Christmas gift. Was looking to get my hands over these guy for a long time. It's smaller than I expected and wow those clicky buttons. Ya I know. My opsec is screwed anyway.
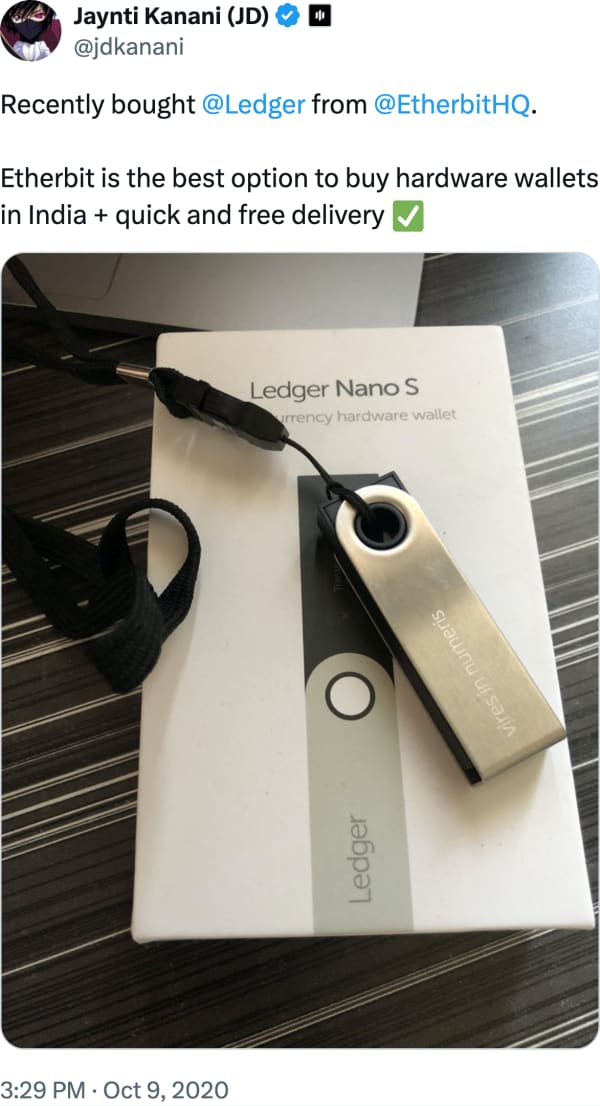
Read full review on XRecently bought @Ledger from @EtherbitHQ . Etherbit is the best option to buy hardware wallets in India + quick and free delivery
Read full review on XYes @EtherbitHQ is the best place buy hardware wallet in india
Read full review on XBought @safepal X1 hardware wallet from @EtherbitHQ My personal opinion which i share with the team too. I got delivery within the expected time and the most importantly their packaging was brilliant and secure. It was way better than phone deliveries. Thanks
Read full review on XCryptos should only be stored in Hardware Wallets. They are the best @EtherbitHQ Good collection, safe courier and must say extremely prompt service. Great going guys!!!!
Read full review on X@EtherbitHQ : Get all your hardware including Yubikeys, Trezors, and Ledgers from here, Indian users. Amazing service and an even amazing customer support. Oh, and they delete you data after 45 days of order. How’s that?! 11/10 Not an affiliate, just a happy customer.
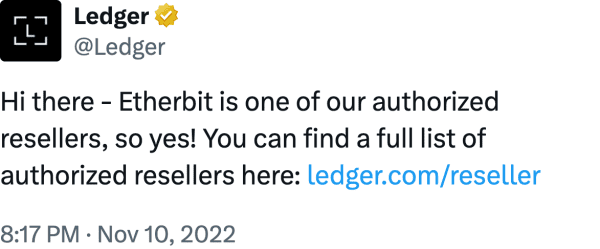
Read full review on XHi there - Etherbit is one of our authorized resellers, so yes! You can find a full list of authorized resellers here: https:// ledger.com/reseller
Read full review on XGot my Trezor One wallet today. Thank you @Trezor and @EtherbitHQ for this ‘Piece Of Mind’ Now my funds are SAFU
Read full review on XGot my first wallet Thankyou @EtherbitHQ @safepal
Read full review on XGot my first #hardwareWallet thanks @safepal and @EtherbitHQ
Read full review on XMy 1st priority always.. @EtherbitHQ Even I recommended too many frndzz and family members .. And I am very happy with your service ... Thnq @EtherbitHQ Proud
Read full review on XOrder on it's way I trust Etherbit i have bought other Products from Etherbit in past
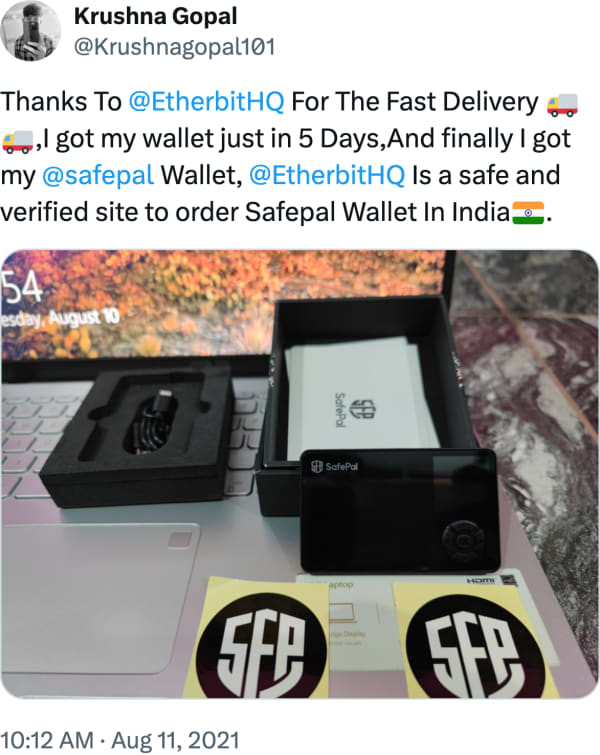
Read full review on XThanks To @EtherbitHQ For The Fast Delivery,I got my @safepal wallet just in 2 Days, @EtherbitHQ Is a safe and verified site to order Safepal Wallet In India.
Read full review on XTowards self-custody & secure hodling Bought Ledger Nano X from @EtherbitHQ with Free Express Shipping #Ledger #Etherbit #India #NotYourKeysNotYourCoins #IamSecure #HomeOfHodlers #Bitcoin
Read full review on Xgives you the best rates and #1 seller of hardware wallets in India.
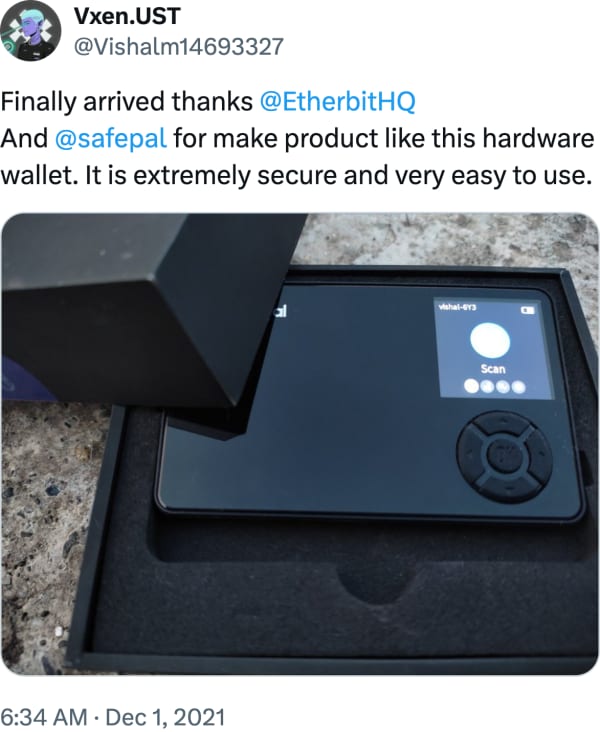
Read full review on XFinally arrived Thanks @EtherbitHQ for Safepal S1
Read full review on XBest part of buying your hardware wallet from @EtherbitHQ is that they take your privacy very seriously and delete your data from database once the wallet is delivered.
Read full review on XHi, Etherbit is legit You can find a list of all our official resellers here
Read full review on XIndia embraces #massadoption There are lots of businesses that offer #BTC payments to clients: Food: @atheynallatha IT & Tech: @HeptagonTech Cars: @mytruebil #Crypto: @Unocoin , @EtherbitHQ Decor: @TheRugRepublic More in our new article https:// nowpayments.io/blog/companies -that-accept-bitcoin-payments-in-india …
Read full review on XOkay !! Thnx @EtherbitHQ for your Prompt reply and support .
Read full review on XHi @qbdx11 - yes, Etherbit is an official Ledger reseller. You can find a full list of approved resellers on our website:
Read full review on XBought Two Ledger Nano S Hardware Wallets from @EtherbitHQ https:// etherbit.in
Read full review on X@EtherbitHQ thank you....I received my device
Read full review on XThanks to you! Just bought from you guys last month and couldn’t be happier
Read full review on XCryptocurrency can also be stored in the Hardware Wallets, which are more safer than the electronic wallets & cryptocurrency exchanges. @EtherbitHQ , Surat-based startup initiated by @harshjv & Dhvani, imports the hardware wallets & helps the Indian investors in terms of storage.
Read full review on XThank you @EtherbitHQ for the replacement of my Ledger Nano X. Guys anyone looking to purchase a hardware wallet in India, Etherbit is your best bet. They are authorized resellers of ledger. Cheap + quick delivery and saves you from hassles of custom!
Read full review on XPls try to connect @gridplus with @EtherbitHQ so that all indians can get safe access to etherbit is a reseller of all type of hardware wallet And etherbit should also make effort to connect with gridplus in order to bring the tech to its customers
Read full review on XThanks for the gift @EtherbitHQ ! The @Ledger Nano X is just amazing.
Read full review on XGiveaway time To celebrate India's 71st #RepublicDay, we're giving away a Ledger Nano S to 3 lucky people who: Retweet this tweet Reply & mention 2 friends Follow @WazirXIndia & @EtherbitHQ Valid for 24 hours!
Read full review on XBought another @Trezor from @EtherbitHQ .Super fast delivery + lowest price in india. These guys are doing god's wok by facilitating easier access to #bitcoin hardware wallets for . I'd highly reccomend them to anybody in india , searching for a trusted vendor
Read full review on XHi, @EtherbitHQ is one of our long-term reseller partners. They are % legit! https:// trezor.io/resellers/
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XWhat a beauty… #Bitcoin @theBLOCKCLOCK @Coinkite @EtherbitHQ
Read full review on XYep! It's time to store few #ONE #MATIC #VET #THETA in secure way. Thanks @safepal @EtherbitHQ @binance
Read full review on XReceived my @safepal Thanks to @EtherbitHQ
Read full review on XBought Ledger Nano S Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XComing soon ...stay connected #Bitcoin @EtherbitHQ @theBLOCKCLOCK @Coinkite
Read full review on XLook what’s here! A safer place for crypto @Ledger Shout out to @EtherbitHQ for such smooth and fast service! #NFT #NFTs #cryptocurrency #Crypto #LedgerWallet #CryptoWallet
Read full review on XHi - yes, Etherbit is one of our approved resellers. You should only ever buy your Ledger from our official website, or via one of these approved resellers - you can find a full list on our website at:
Read full review on XTowards self-custody & secure hodling Bought Trezor Safe 3 from @EtherbitHQ with Free Express Shipping #Trezor #Etherbit #India #NotYourKeysNotYourCoins #IamSecure #HomeOfHodlers #Bitcoin
Read full review on XYou can buy hardware wallets from http:// etherbit.in . Ledger and Trezor are trusted brands.
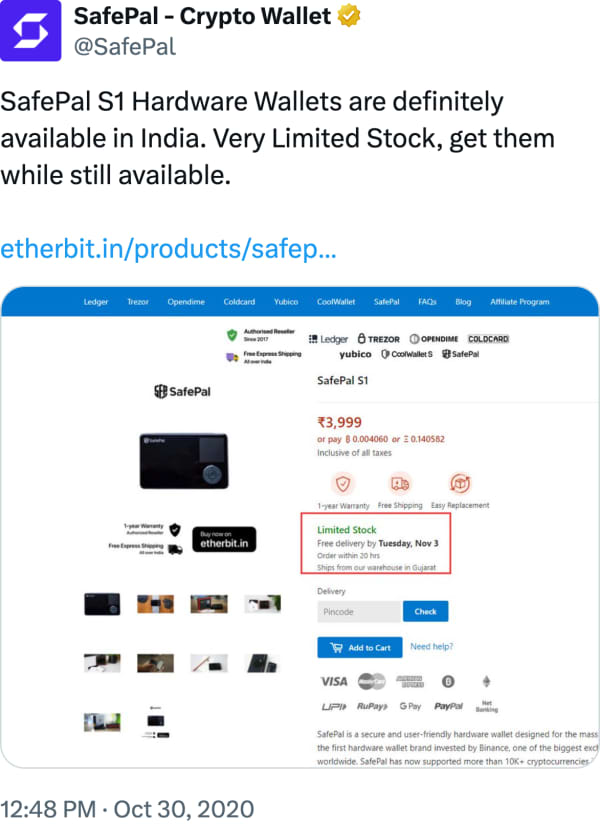
Read full review on XSafePal S1 Hardware Wallets are definitely available in India. Very Limited Stock, get them while still available. https:// etherbit.in/products/safep al-s1?r=1563b69f …
Read full review on XThank you @EtherbitHQ — I received it this evening, need to do hardware integrity test before loading it up. I hope that doesn’t void warranty!
Read full review on Xhttps:// etherbit.in/?r=f3783a43 Anyone living in India and working with cryptocurrency needs to have a hardware wallet. If you want the best hardware wallet, you can get it from the official website here. @EtherbitHQ
Read full review on XJust recieved! @safepal courtesy of @EtherbitHQ
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XIf you are in #India and struggling to buy Trezor One to protect your crypto then try either bit. Buy now https:// etherbit.in/products/trezo r-one?r=c5049c1d … #dogecoin #Bitcoin #USDT #etherium
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on X@EtherbitHQ thanks for delivering essentials
Read full review on XIf there are genuine resellers like @EtherbitHQ then i will surely buy from them...ohh i already bought one from them in 2017 and its working as expected
Read full review on XWhere to purchase Hardware wallets in India? Answer: @EtherbitHQ Link: https:// etherbit.in/?r=70a8e402 #Bitcoin #hardwarewallet
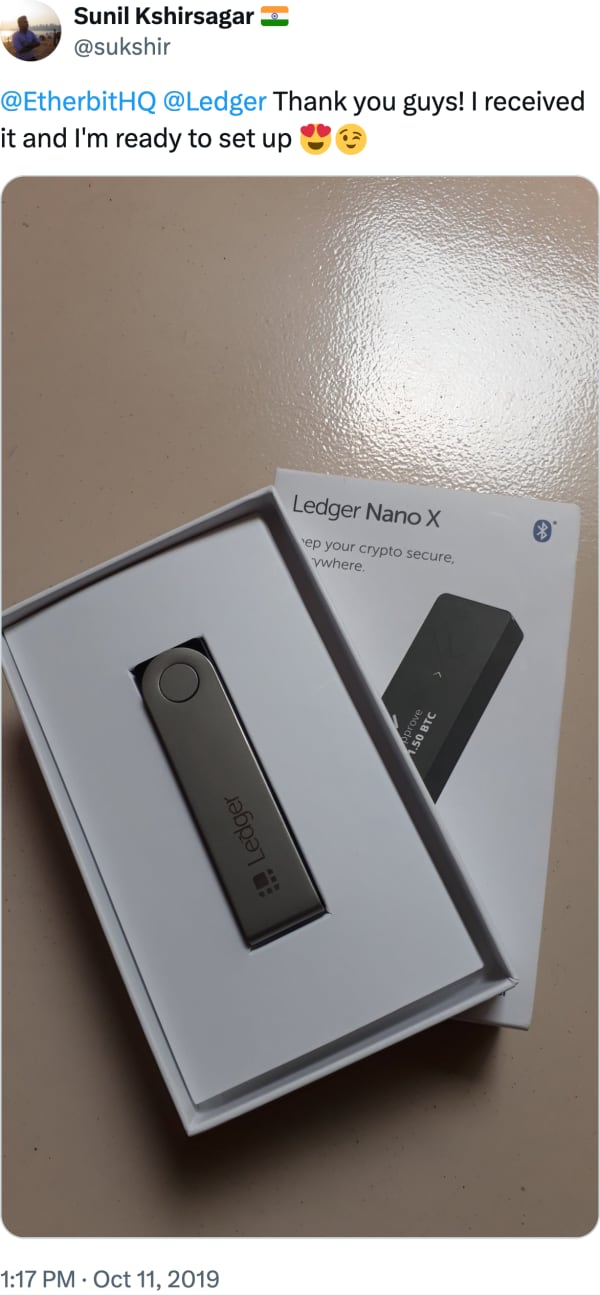
Read full review on X@EtherbitHQ @Ledger Thank you guys! I received it and I'm ready to set up
Read full review on Xtoday i received the order details by sms..thanks for shipping it promptly.
Read full review on XFor my love towards Crypto & Blockchain. @Ledger @EtherbitHQ #crytocurrency #blockchains #btc #eth
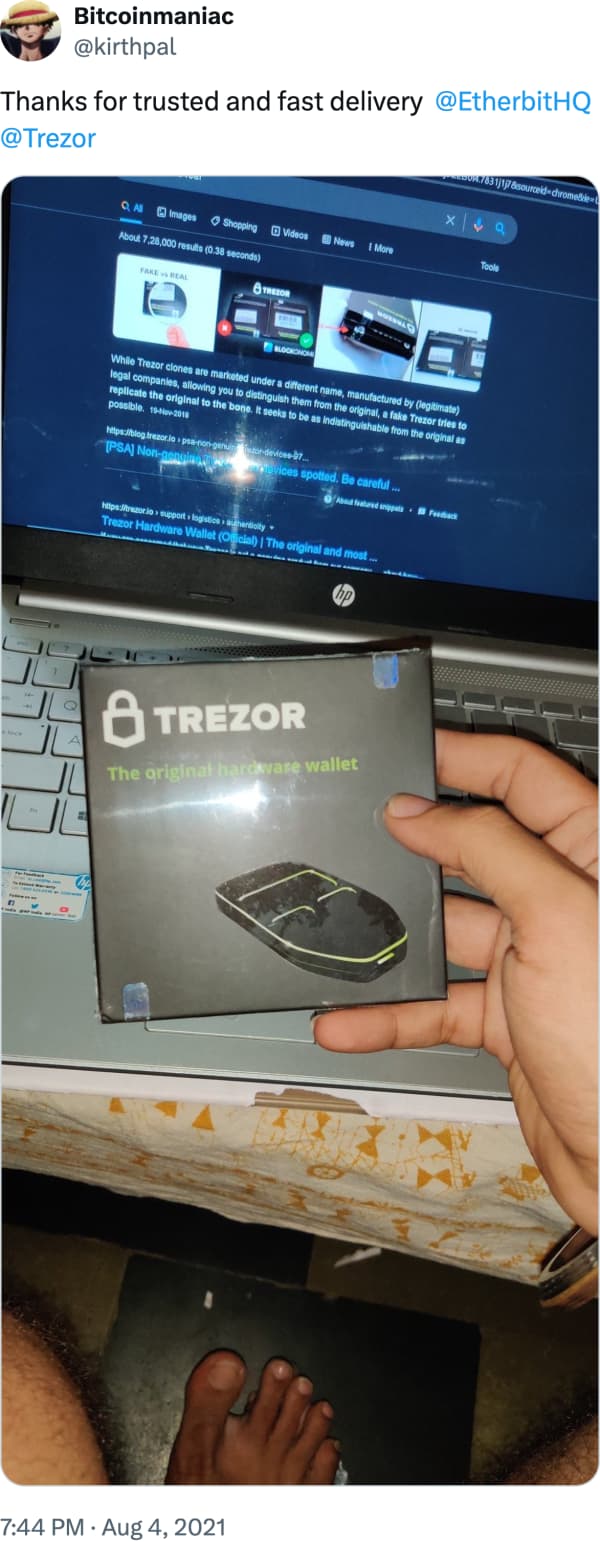
Read full review on XThanks for trusted and fast delivery @EtherbitHQ @Trezor
Read full review on XThank you so much for tagging my tweet and for your support. You really made my day. I really appreciate the services provided by Etherbit. I received positive feedback from many of my friends too. Thank you for making hardware wallets easily available to people in India.
Read full review on X@kvmadhukumar u can placed order now!!! Thnx for your Prompt Reply @EtherbitHQ
Read full review on XGuess what is here @prado0044 Thanks @EtherbitHQ #safepal #cryptocurrency
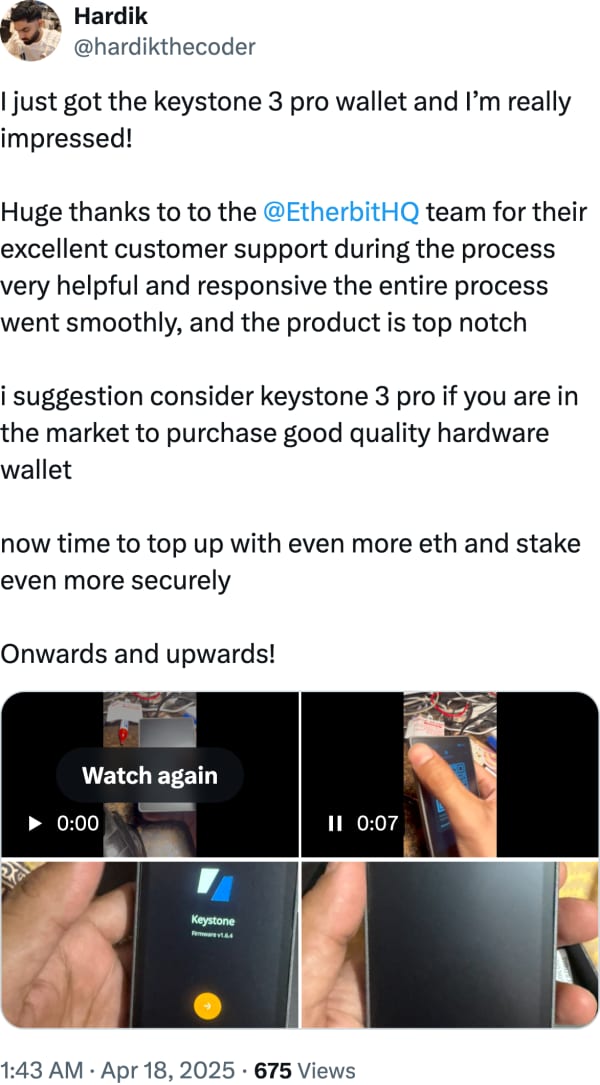
Read full review on XI just got the keystone 3 pro wallet and I’m really impressed! Huge thanks to to the @EtherbitHQ team for their excellent customer support during the process very helpful and responsive the entire process went smoothly, and the product is top notch i suggestion consider keystone 3 pro if you are in the market to purchase good quality hardware wallet now time to top up with even more eth and stake even more securely Onwards and upwards!
Read full review on X2\ hardly 2 days after the order... Received my Trezor... Awesome shipping time by @EtherbitHQ #TREZOR #etherbit #BTC #ETH
Read full review on XPleasantly surprised with how easy @Tangem was to set up. Thank you to @EtherbitHQ for the quick delivery. If anyone wants HW Wallets: https:// etherbit.in/?r=3cf33f27
Read full review on XExcellent!! Thanks for pointing out that page.. I'll use it to recommend @EtherbitHQ to my pals in India looking to buy a hardware wallet.. Hat tip to @elviric ..
Read full review on X@EtherbitHQ Thank you My first Hardware wallet @safepal
Read full review on XThank you so much @EtherbitHQ for the quick delivery of my @safepal wallet
Read full review on XNot your keys, Not your crypto… just received my device.. fast delivery..thanks @EtherbitHQ
Read full review on XHi, @EtherbitHQ is our official reseller. You can find list of all our resellers here: https:// trezor.io/resellers Please let us know if you need any assistance regarding this order, but we firmly believe that Etherbit will deliver the order very soon!
Read full review on XI made a payment for my hardware wallets via #ETH in @EtherbitHQ and loved the smooth experience. Cheers to that
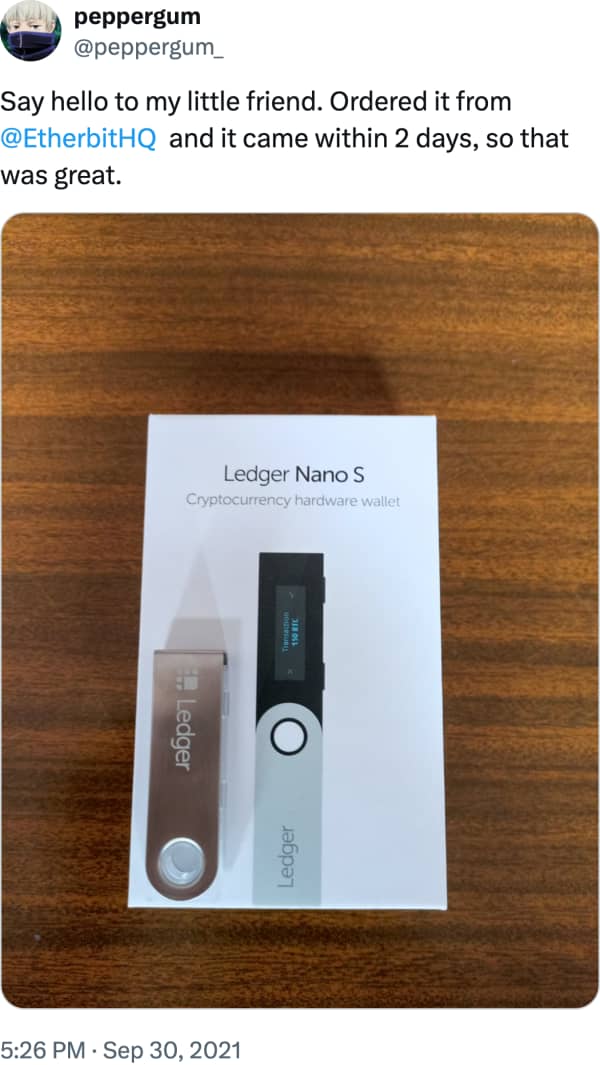
Read full review on XSay hello to my little friend. Ordered it from @EtherbitHQ and it came within 2 days, so that was great.
Read full review on XBought Ledger Nano S from @EtherbitHQ https:// etherbit.in
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XHey - indeed, getting a hardware wallet would be ideal! We have official resellers like Etherbit located in India that you can buy from!
Read full review on XJust bought a hardware wallet device using usdc on @EtherbitHQ We are really in the magic internet money era Most of my regular purchases are being made using crypto cards too. This is the coolest thing. As crypto maxi.
Read full review on XBought Bitcoin Mug from @EtherbitHQ https:// etherbit.in
Read full review on XThanks @EtherbitHQ for quick delivery. Received the package safe and sound. Cheers!! #VocalForLocal @Ledger
Read full review on X#39 Always keep most of your crypto safe & offline in a cold storage wallet. Be safe than sorry. I bought mine at http:// etherbit.in @EtherbitHQ (For India)
Read full review on XEtherbit is an awsm online shops for buying this device such an unbelievable prices...hats off to u guys
Read full review on XYes i know, but without any seller name and with so many cases on Reddit/X, why risk it? For safety just buy from Ledger or Etherbit, Also in India no one is going to help if you lose money. Best to stick with safer options.
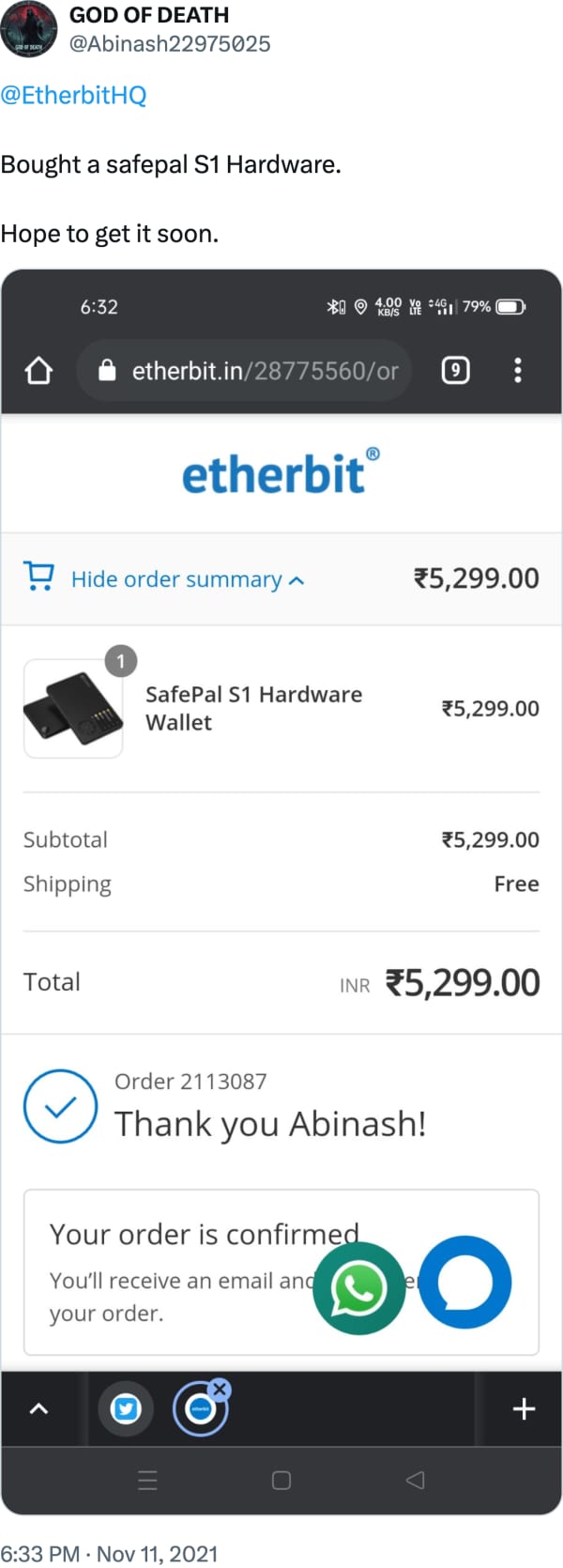
Read full review on X@EtherbitHQ Bought a safepal S1 Hardware. Hope to get it soon.
Read full review on XIts really amazing @EtherbitHQ @Ledger
Read full review on XFinally got the @safepal wallet from @EtherbitHQ without having to worry about the import duties #SFP #ETHERBIT
Read full review on XBought Ledger Nano S from @EtherbitHQ https:// etherbit.in
Read full review on XReceived my trezor 5 @Trezor today! Thanks to @EtherbitHQ for the sweet deal
Read full review on XBought from @EtherbitHQ at 5999₹ because of the trust and reliability. But a must have product!! Still never hold your entire crypto in one ledger. Always distribute your holdings!
Read full review on XReward will be physically via @EtherbitHQ
Read full review on XFinally arrived thanks @EtherbitHQ And @safepal for make product like this hardware wallet. It is extremely secure and very easy to use.
Read full review on XThanks @EtherbitHQ for superfast delivery of my first @safepal hardware wallet I just loved this super cool wallet
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XI am looking forward to buy a safepal Wallet from @EtherbitHQ
Read full review on XBought my first hardware wallet @Ledger nano s plus from @EtherbitHQ . Received it in just 3 days, etherbit is the best place to buy wallets in India. genuine product + fast delivery thank you @EtherbitHQ , I have ordered a new evolution of money hoddie too
Read full review on XThanks to @EtherbitHQ for Crypto Coin Stickers..
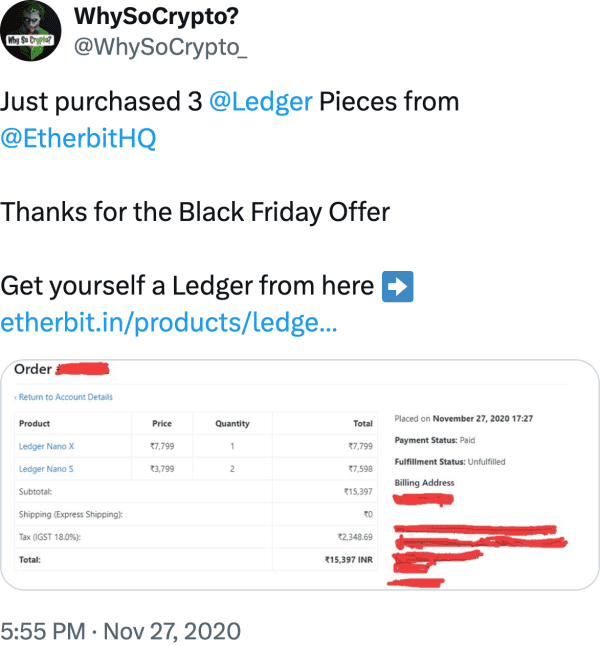
Read full review on XJust purchased 3 @Ledger Pieces from @EtherbitHQ Thanks for the Black Friday Offer Get yourself a Ledger from here https:// etherbit.in/products/ledge r-backup-pack-ledger-nano-x-ledger-nano-s?r=5845d399 …
Read full review on XThanks @EtherbitHQ I first thought you were a scam lol but no you'll be my go to for all crypto needs now.
Read full review on XHow it started …. Thanks, @Coinkite for this wonderful piece @EtherbitHQ for shipping it home… #Bitcoin
Read full review on X@safepal @EtherbitHQ Safepal You Build A Stone Un Breakable Lol
Read full review on XThanks To @EtherbitHQ For The Fast Delivery ,I got my wallet just in 5 Days,And finally I got my @safepal Wallet, @EtherbitHQ Is a safe and verified site to order Safepal Wallet In India.
Read full review on XHodl Gang let's goo @Ledger Thanks for quick delivery @EtherbitHQ
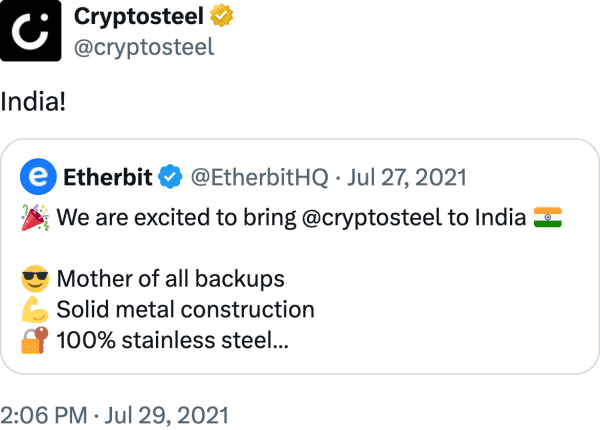
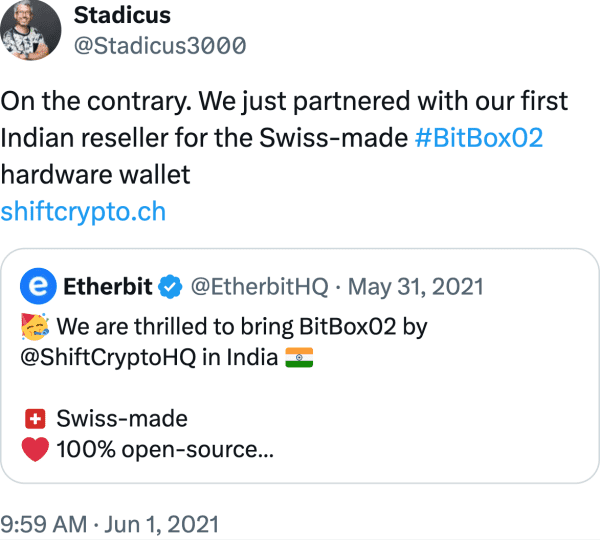
Read full review on XOn the contrary. We just partnered with our first Indian reseller for the Swiss-made #BitBox02 hardware wallet https:// shiftcrypto.ch
Read full review on XYou can buy Ledger through @EtherbitHQ . They delete user data after 45 days
Read full review on X@EtherbitHQ I love etherbit. It Is the Best & Genuine site in India For Hardware Wallets.
Read full review on X@EtherbitHQ ty for shipping @Ledger nano orders early
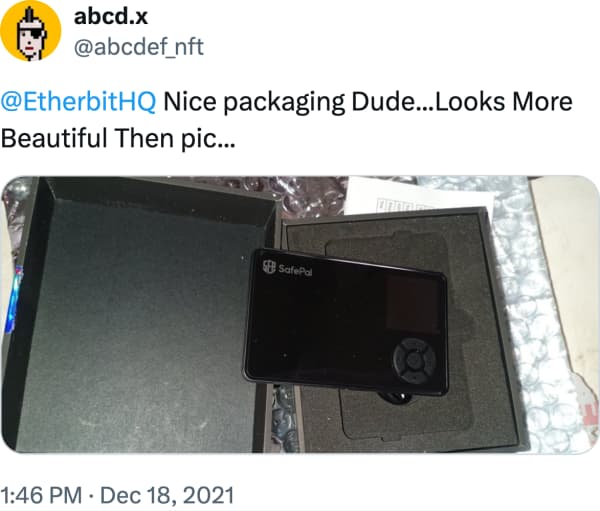
Read full review on X@EtherbitHQ Nice packaging Dude...Looks More Beautiful Then pic...
Read full review on XThanks @EtherbitHQ Be a own banker
Read full review on XGot my hardware wallets after a long wait.. @safepal @EtherbitHQ
Read full review on X@Ledger thanks for the product. Please tie-up with the steller,Shiba etc so that token are directly supported in Ledger Live. @EtherbitHQ
Read full review on Xalready buyed 2 ledger nano from @EtherbitHQ , superfast delivery and trustable sourse. @Victory2Crypto_ @Crypto2devi_ @djwalababu8
Read full review on X@EtherbitHQ No Words....thanks @EtherbitHQ
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
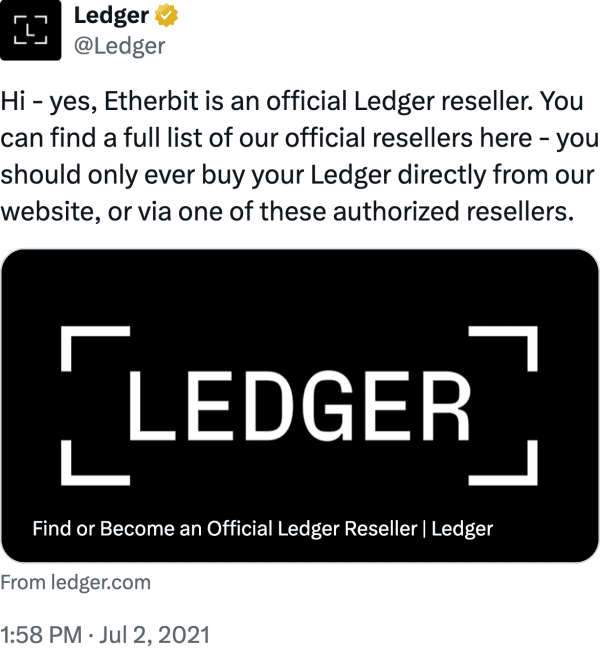
Read full review on XHi - yes, Etherbit is an official Ledger reseller. You can find a full list of our official resellers here - you should only ever buy your Ledger directly from our website, or via one of these authorized resellers.
Read full review on XWelcome to millions of things for #Bitcoin, @EtherbitHQ ! https:// spendabit.co/go?q=ledger+na no+x … @Ledger
Read full review on X@EtherbitHQ any plans to support @gridplus lattice? Would love to use the Lattice here in India.
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
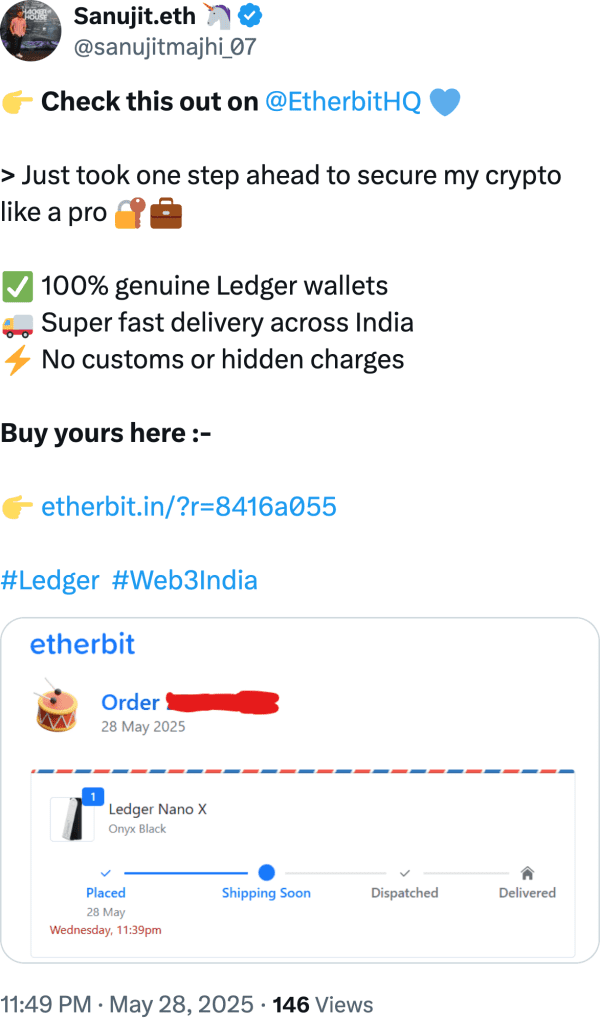
Read full review on XCheck this out on @EtherbitHQ > Just took one step ahead to secure my crypto like a pro 100% genuine Ledger wallets Super fast delivery across India No customs or hidden charges Buy yours here :- https:// etherbit.in/?r=8416a055 #Ledger #Web3India
Read full review on XThank you for prompt reply. i am placing order from them
Read full review on XReceived my giveaway prize of SafePal S1 HW Wallet from @EtherbitHQ Express delivered Thank you Etherbit Team
Read full review on XThanks @EtherbitHQ Today Receive My @safepal Hardware Wallet Very Good Quality I Just Miss Type C Charging Port And Everything Ok
Read full review on XBought Crypto Stickers 12-Pack and Ledger Nano S from @EtherbitHQ https:// etherbit.in
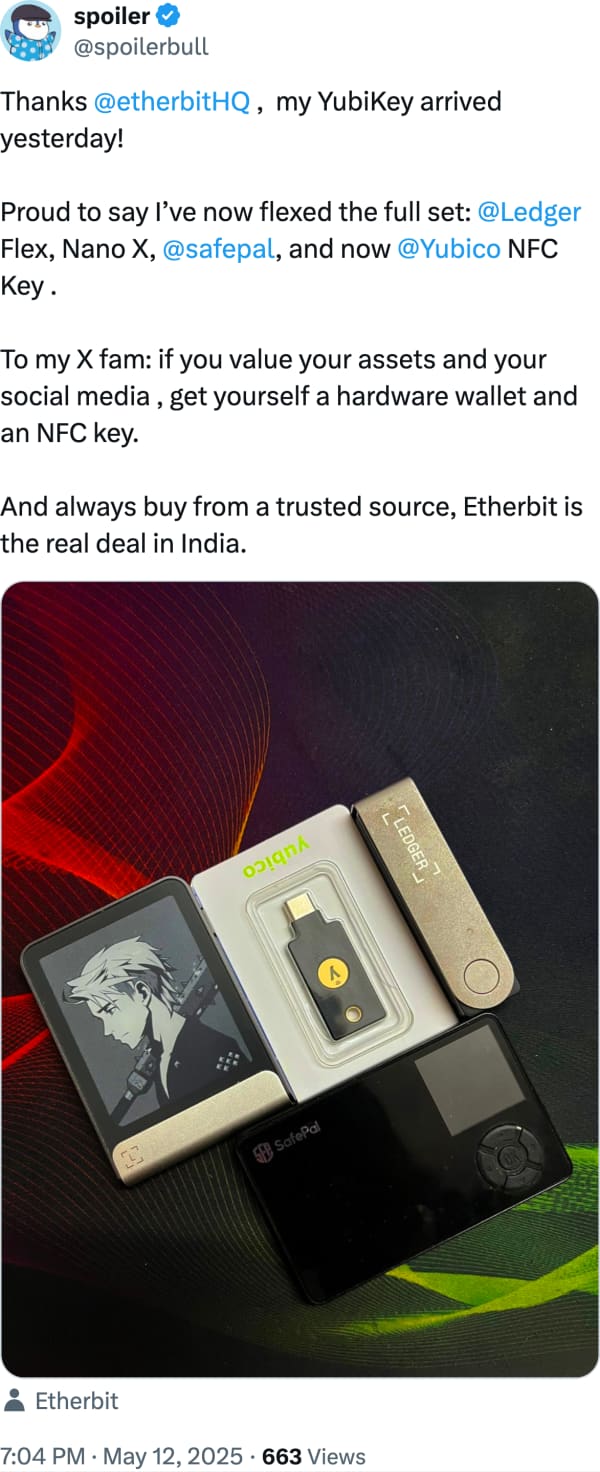
Read full review on XThanks @etherbitHQ , my YubiKey arrived yesterday! Proud to say I’ve now flexed the full set: @Ledger Flex, Nano X, @safepal , and now @Yubico NFC Key . To my X fam: if you value your assets and your social media , get yourself a hardware wallet and an NFC key. And always buy from a trusted source, Etherbit is the real deal in India.
Read full review on XBought SafePal S1 Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XJust ordered a @safepal through http:// etherbit.in .
Read full review on Xthanks for providing the crypto devices to us indians. good to see homegrown brand giving such wider collection of devices. my first device was also from etherbit .
Read full review on X@EtherbitHQ .. received my first hardware wallet. Thanks
Read full review on XI received my safepal @EtherbitHQ @safepal Really different and amazing hardware wallet
Read full review on X@EtherbitHQ @safepal thanks for fast delivery. Very compact and light weight wallet. Good service thank you.
Read full review on XGet your Cryptotags in India now from Etherbit!
Read full review on XHi - yes, Etherbit is one of our approved resellers. You can find the full list here:
Read full review on XBought Ledger Nano S Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XBought Ledger Nano S Hardware Wallet from @EtherbitHQ https:// etherbit.in
Read full review on XAlso buy through @EtherbitHQ which is one of the official reseller in India to save on custom duty.
Read full review on X